66
BizVoice/Indiana Chamber – July/August 2017
By Matt Ottinger
Beware of Risky Behaviors, Sophisticated Threats
BEHIND THE
CYBER CURTAIN
WannaCry. It’s the aptly-named
computer virus that, according to
European law enforcement agency
Europol, hit 150 countries and
infected 200,000 machines in
May. The ransomware cryptoworm
attack targeted computers using
the Microsoft Windows operating
system by encrypting data and
demanding users pay to recover it.
Ransomware is just the latest
iteration of computer hacking that
has businesses – both large and
small – searching for advice and
protection.
“For the bad guys, it’s a low-risk, potentially
high-reward endeavor,” contends Chuck Cohen,
Indiana State Police captain and director of
the Indiana Intelligence Fusion Center (IIFC).
“It’s a phenomenon we’ve seen with regularity
over the last several years. But Indiana
businesses and government organizations tend to
be high-value targets because they hold
information that is critical to run their operations.”
Trojan viruses, phishing, malicious bait
and switch programs and cookie theft are
other common hacking techniques. Denial of
service attacks can also be an instrument of
destruction for businesses.
Sid Bose, an attorney in Ice Miller’s
Litigation and Intellectual Property Group,
tells the story of such an attack.
“In a smoke screen situation, a company
was getting bombarded with millions of
requests through its online web portal from
different computers that had been compromised
by malware, which essentially made them
little drones,” he recalls. “It basically brought
their network to a grinding halt because it
couldn’t handle the load from these attacks.
“On its face, the motivation was thought
to disrupt the operation of the portal, but an
investigation showed that the attack was a
smoke screen to pull money out of the company’s
bank account. Those are sophisticated attacks.”
Breaking bad behavior
Vulnerability is often most evident in
human frailties rather than technical
weaknesses, according to experts.
“There’s a popular saying: Amateurs hack
computers but professionals hack people,”
Bose relays. “Phishing is so successful because
it takes advantage of our behaviors and the
desire to want to be useful when someone
makes a request of you.”
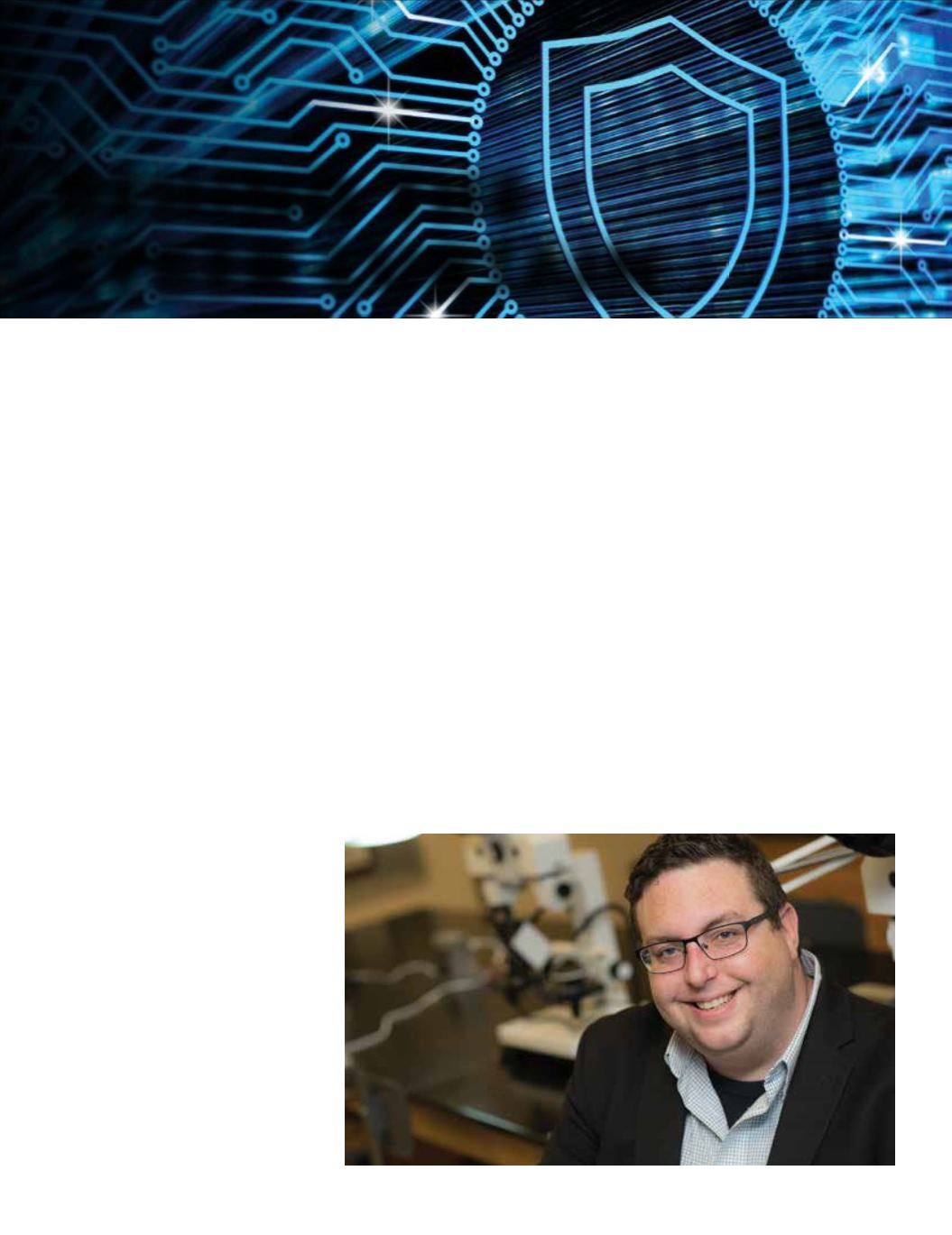
Bill Mackey, an assistant professor at
Indiana State University (ISU), is launching
new courses (Intelligence Analytics and
Cybercriminology) to train students in the
behavioral aspects of cybersecurity. Mackey
also owns Alloy Cybersecurity – a firm that’s
hiring ISU students as interns to offer real
world experience in the field. He outlines
behavioral-based approaches to exposing a
company’s vulnerabilities.
“We look at names, email addresses and
basic information from web sites,” Mackey
notes, explaining phishing efforts will often
relate to a person’s hobbies or a company’s
industry. “Using open source intelligence,
we’ll find out how active you are online and
how much information you’ve divulged that
we can access. Then we’ll try to use that
against you. It might go beyond just the
standard phishing email from corporate
saying, ‘Click on this link.’
“We can get incredibly personal,” he
adds. “If we know John Doe drives a certain
car or eats at a certain place or donates money
to a certain group, that will be exploitable
and a vulnerability we could attack.”
Mackey also says training ISU students to
be behavior analysts will help close a critical
knowledge gap.
“What I’ve found is that businesses are
“A problem we see is that a business
may have taken great steps toward
security and computer hygiene but
their vendor hasn’t.”
– Bill Mackey